Offensive Security & AppSec
Symosis arms your organization with proactive, adversary-level security testing and software integrity services—sharpening defenses before attackers can strike.
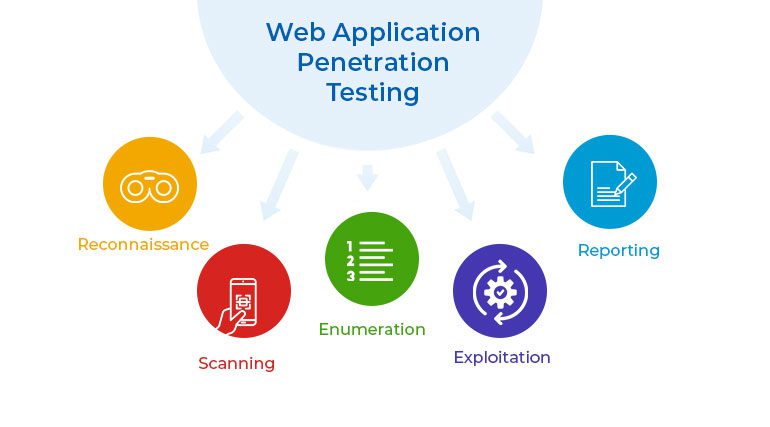
Web & Mobile Application Penetration Testing
The Problem:
Undetected vulnerabilities in web or mobile apps can lead to data breaches, business disruption, and compliance failures.
Our Approach:
We simulate real-world attacks using OWASP Top 10 methodologies, API fuzzing, credentialed and unauthenticated testing, and platform-specific reviews.
How It Helps:
You receive prioritized vulnerability reports, remediation recommendations, and concrete proof of secure app deployment.
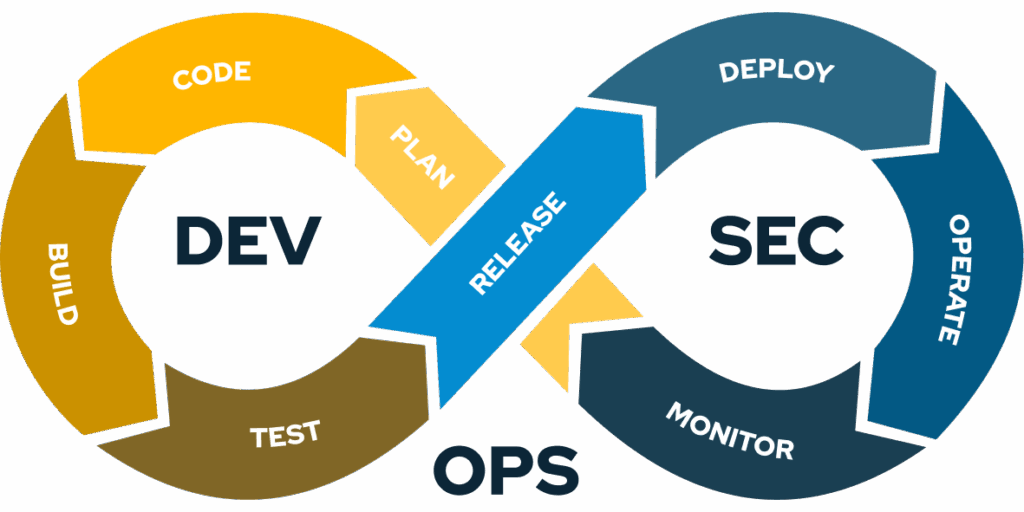
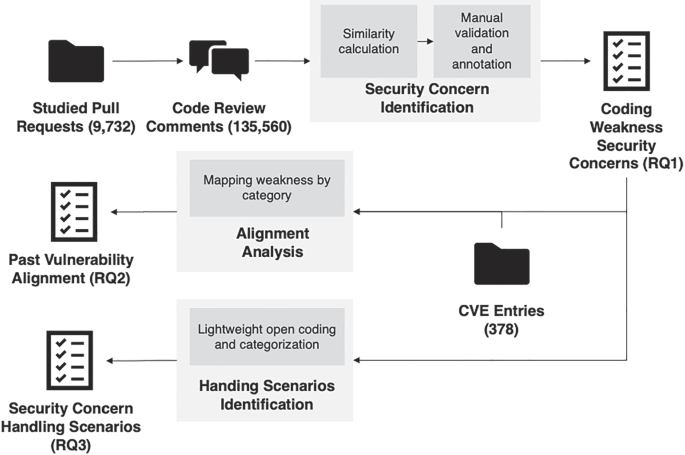
Secure Code & Architecture Reviews
The Problem:
Security flaws often surface late in development, increasing remediation cost and risk of flawed designs.
Our Approach:
We conduct in-depth code reviews, threat-model-based architecture assessments, and SDLC integration using OWASP SAMM.
How It Helps:
You proactively identify and mitigate risky coding patterns or architectural weaknesses before release.
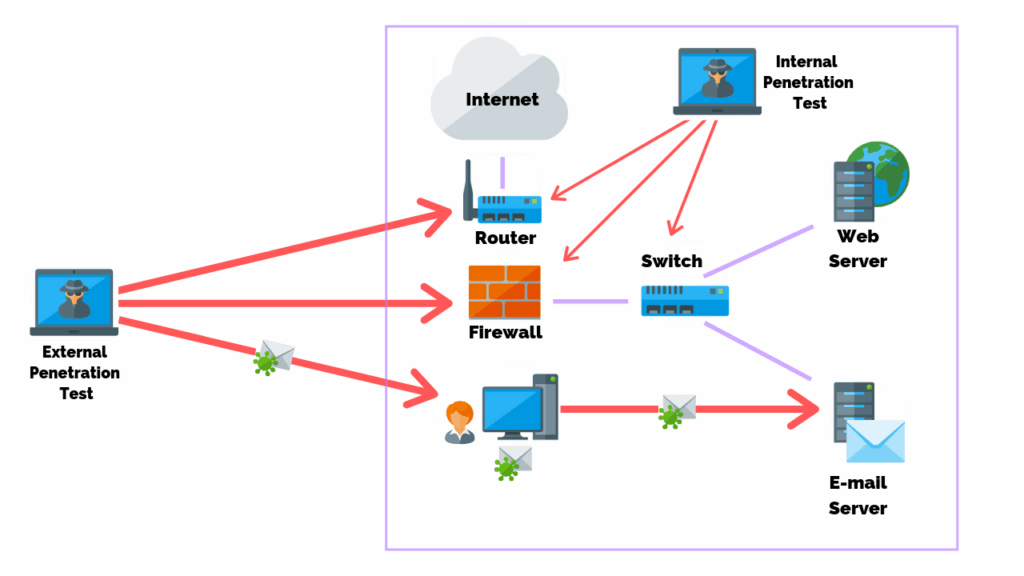
Network Penetration Testing (External & Internal)
The Problem:
Lateral attack paths, misconfigured internal networks, and unpatched systems can compromise entire environments.
Our Approach:
Symosis performs external and internal pen tests with post-exploitation to simulate real intrusions and identify attack chains.
How It Helps:
Gain clarity on exploitable paths, hardened network defenses, and evidence-backed risk mitigation.
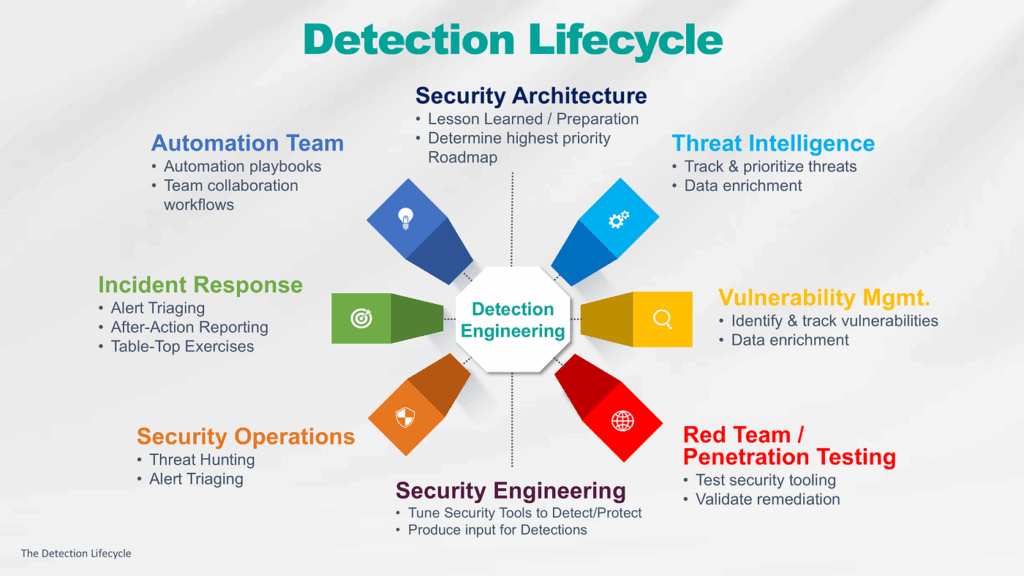
Red Team & Adversary Emulation
The Problem:
Security teams often lack exposure to advanced, stealthy threats until it’s too late.
Our Approach:
We run full-scope red team exercises aligned to MITRE ATT&CK emulations, cloud pivot testing, and operational stealth techniques.
How It Helps:
You test detection, response, and resilience capabilities — leading to stronger defense postures and better incident readiness.

Threat Modeling Workshops
The Problem:
Teams often overlook deep-rooted threats without structured threat modeling and early analysis.
Our Approach:
We facilitate STRIDE and other frameworks in workshops, build data flow diagrams, and identify real-world attack scenarios early.
How It Helps:
IT and development teams better understand application risk, enabling informed design and prioritized security investments.
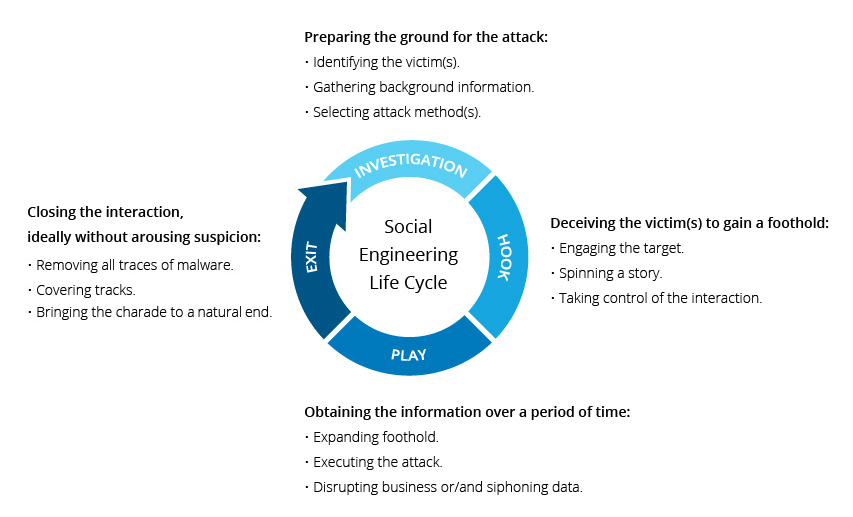
Social Engineering (Phishing, Vishing, Physical)
The Problem:
Employees and processes are common vectors for attacks, without proper awareness or detection.
Our Approach:
We design and execute targeted phishing, vishing, and physical breach tests paired with metrics and training follow-up.
How It Helps:
You measure and improve staff readiness, reduce human error risk, and build a mature security-awareness culture.
Remediation Validation & Continuous Testing
The Problem:
Fixes are often deployed without assurance or tracking — leading to recurring vulnerabilities and ineffective controls.
Our Approach:
Symosis re-tests remediated components, validates compensating controls, and supports continuous testing lifecycles.
How It Helps:
You gain confidence that vulnerabilities are truly resolved — minimizing repeat issues and strengthening overall security hygiene.