Zero Trust Enablement
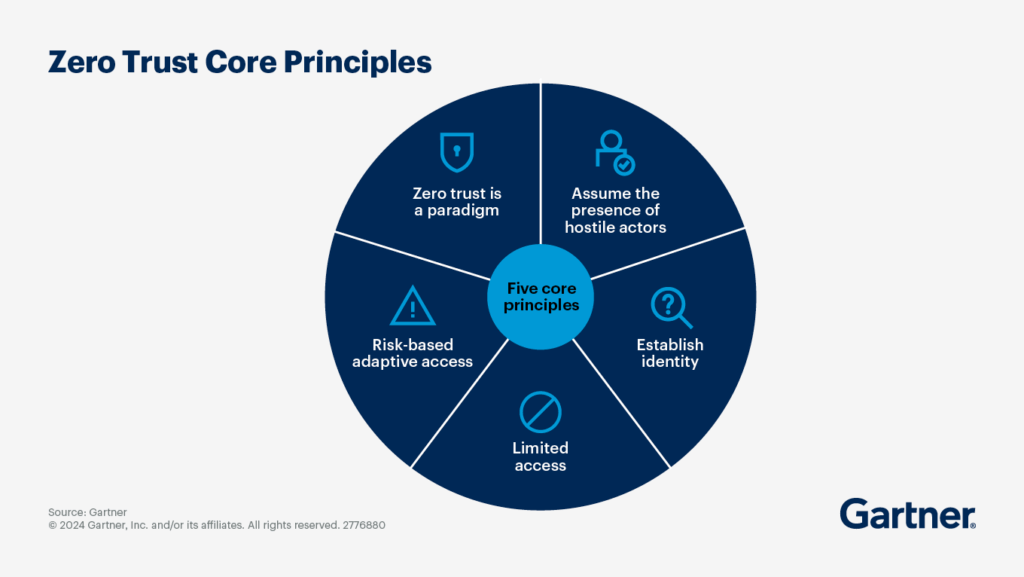
From remote users to cloud workloads, traditional perimeter defenses are no longer enough. Symosis helps organizations adopt a Zero Trust architecture that continuously validates identity, device posture, and context — ensuring only the right people access the right resources, under the right conditions.
We don’t sell software.
Symosis provides independent guidance, implementation expertise, and automation support across your chosen Zero Trust technologies — helping you assess needs, select the right vendors, and deploy effectively.
Problem → Solution
The Problem:
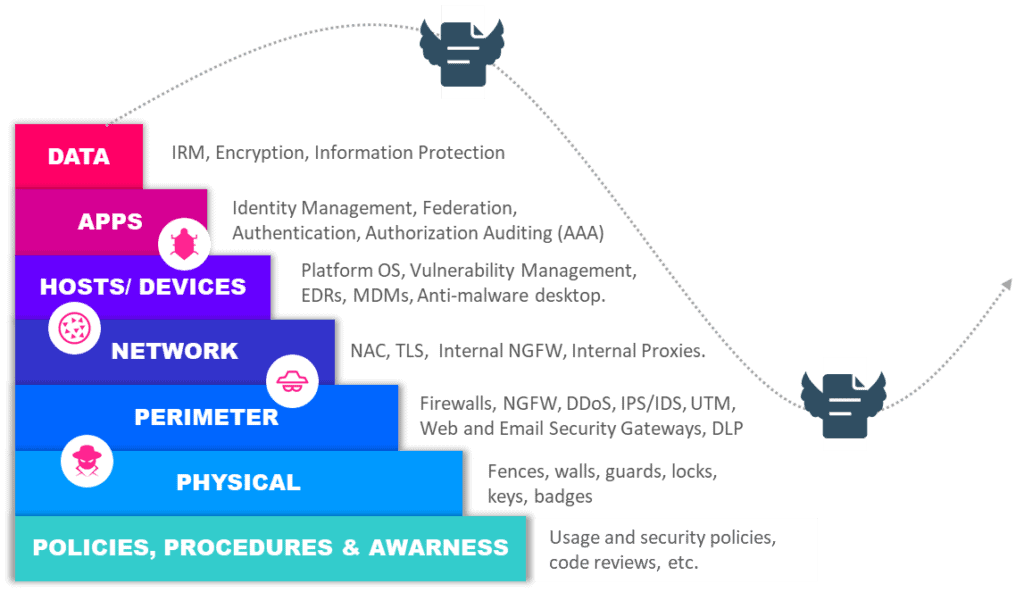
Most security programs still rely on implicit trust, over-permissioned users, and flat network access. Common challenges include:
Overly broad user access and lateral movement risk
Fragmented identity systems (e.g., Okta, Azure AD, legacy LDAP)
Lack of consistent MFA, device posture checks, and segmentation
Disconnected SaaS, IaaS, and on-premise access policies
Our Solution:
Symosis provides architecture, assessment, and execution support for Zero Trust adoption:
Identity and access mapping
Role-based and context-aware policy design
Vendor-agnostic support across Okta, Microsoft, Ping, Netskope, Zscaler, etc.
Posture validation, remediation tracking, and automation
Executive reporting and continuous improvement guidance
We focus on operationalizing Zero Trust — not just documenting it.
Key Focus Areas
Symosis delivers Zero Trust outcomes across five core pillars:
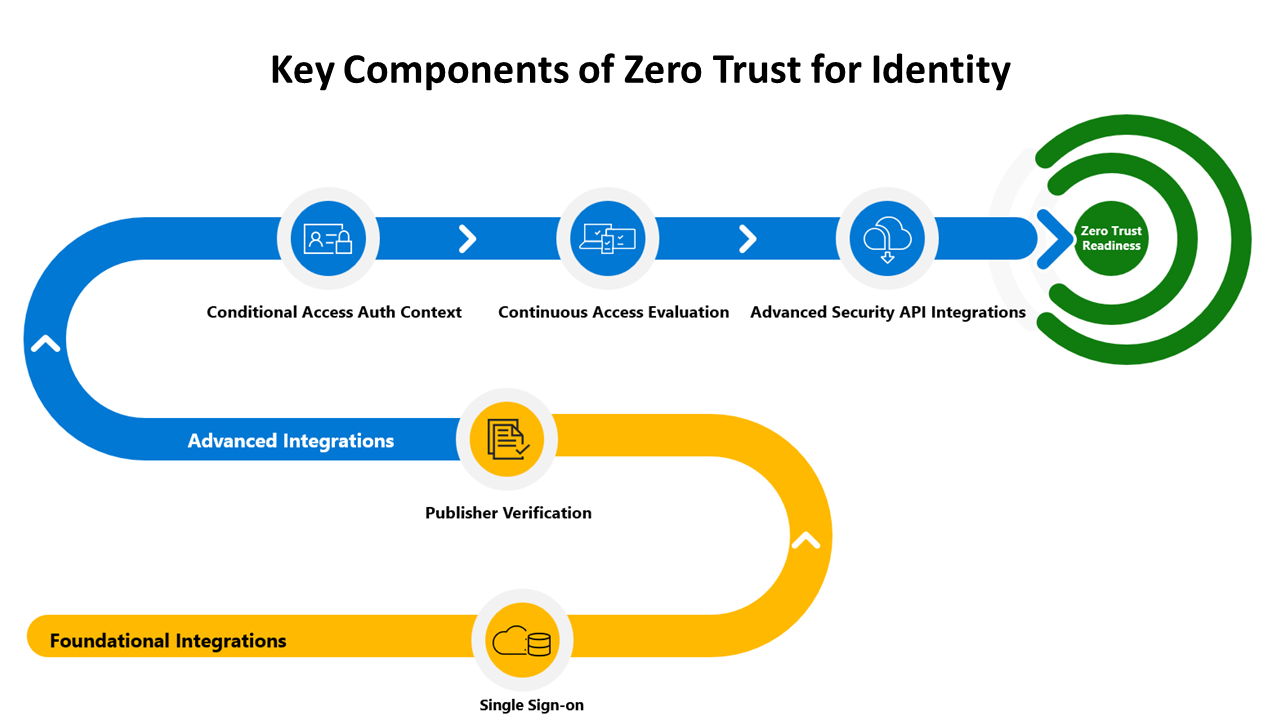
Identity & Access Management
Centralized SSO, MFA, RBAC/ABAC design, SCIM provisioning
Device Trust & Posture
Integration with MDM, EDR, and conditional access enforcement
Network Segmentation & Access Control
SASE/ZTNA design and microsegmentation strategies
Application & SaaS Security
Contextual access controls for Microsoft 365, Salesforce, GCP, etc.
Data & Resource Protection
Least privilege access to data, automated DLP policy enforcement
How It Works – 3 Steps to Zero Trust Confidence
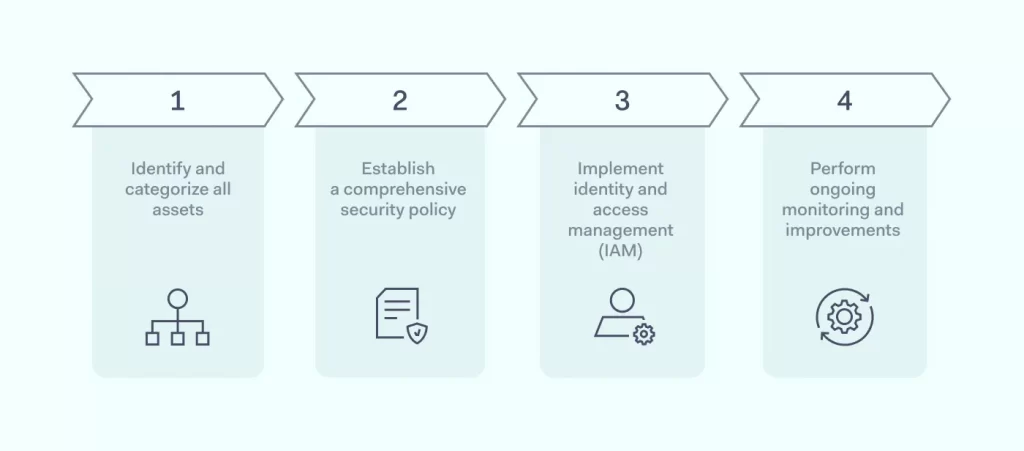
1. Assess
Inventory users, devices, apps, and trust boundaries
Identify gaps across identity, access, network, and posture
Map risks to business processes and crown jewels
2. Design
Develop a Zero Trust architecture blueprint
Recommend vendor platforms and integration layers
Create actionable policy frameworks
3. Operationalize
Implement and integrate policies across tools and teams
Automate posture scoring, drift detection, and reporting
Provide remediation playbooks and lifecycle maintenance
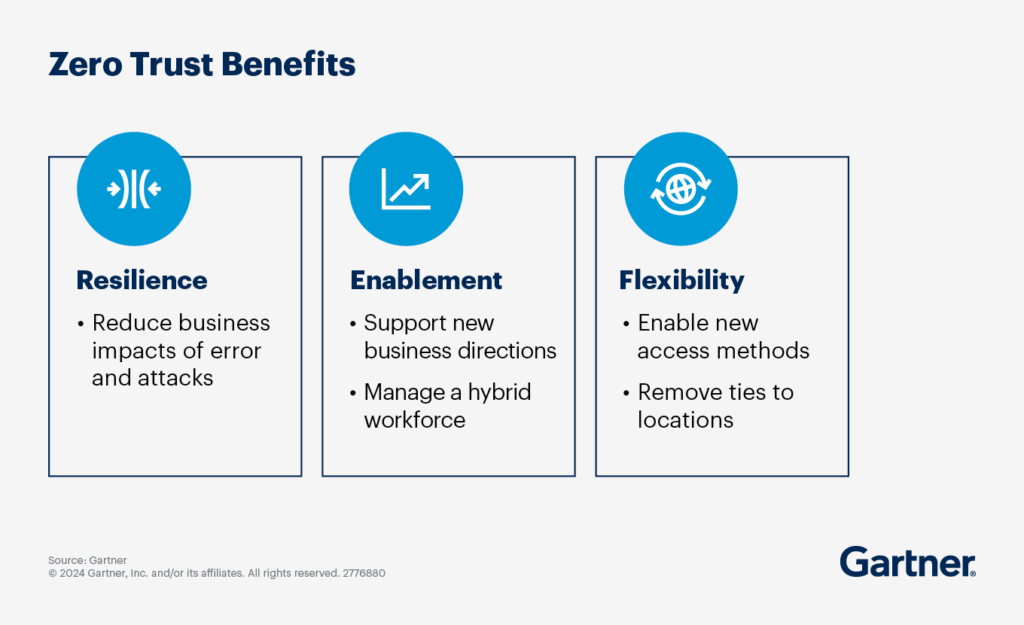
Outcomes
🔐 Identity-based segmentation and reduced lateral movement
👁️ Full visibility into access across hybrid and cloud environments
🧰 Operationalized controls using your existing tools
📊 Maturity scoring and progress tracking for executives