Advisory & Governance Services
Symosis helps organizations align cybersecurity strategy with enterprise goals by embedding risk management, governance, and compliance into executive decision-making.
We provide expert guidance at the intersection of security, leadership, and digital transformation—ensuring your cybersecurity posture supports both innovation and regulatory requirements. Whether you’re establishing foundational governance practices or modernizing risk programs to support AI adoption, our team enables measurable improvements in executive trust, audit readiness, and cyber resilience.
From policy design to board reporting, and from AI governance to third-party risk oversight, Symosis equips you with the frameworks, tools, and insights needed to lead with confidence in a rapidly evolving threat landscape.
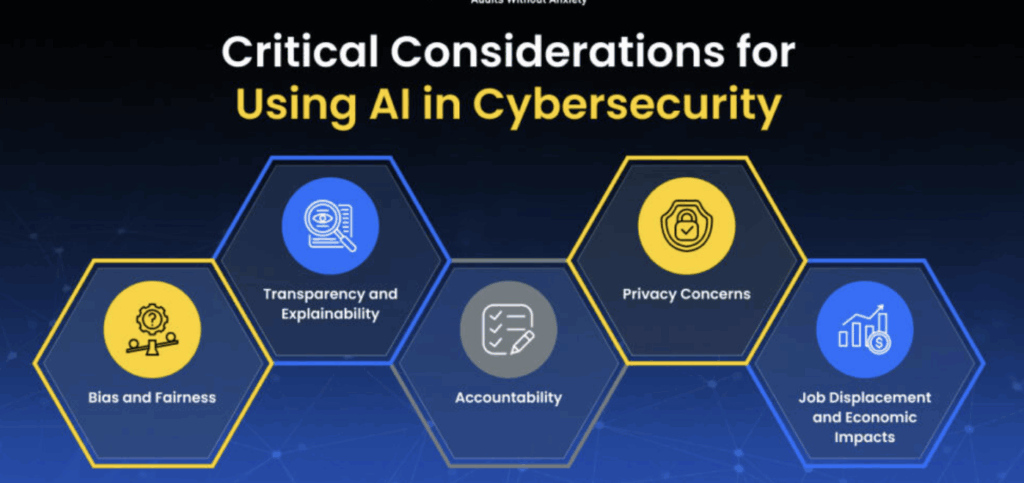
Cybersecurity & AI Strategy
Align AI and security with business outcomes through strategic planning and executive guidance.
Policy Development & Implementation
Create audit-ready security and AI policies tailored to your business and compliance needs.
vCISO / Fractional CISO
Get experienced security leadership without the overhead of a full-time hire.
Regulatory Compliance
Navigate HIPAA, PCI, NIST, and other frameworks with streamlined compliance support.
Business Continuity & Disaster Recovery
Build and test resilient BCP/DR plans to protect operations and reduce downtime.
Privacy Programs
Operationalize GDPR, CCPA, HIPAA, and AI privacy protections with automated workflows.
Cybersecurity & AI Strategy
The Problem:
Many security programs lack business alignment. AI initiatives are moving fast, but without security leadership or clear priorities, they result in silos and budget shortfalls.
Our Approach:
We define and deliver strategic roadmaps that:
Integrate AI risk, zero trust, and business resilience
Provide CISO-level guidance without full-time headcount
Align initiatives to executive and board priorities
How It Helps:
You get stakeholder buy-in, clear direction, and funding clarity for both traditional and AI-driven cybersecurity programs.
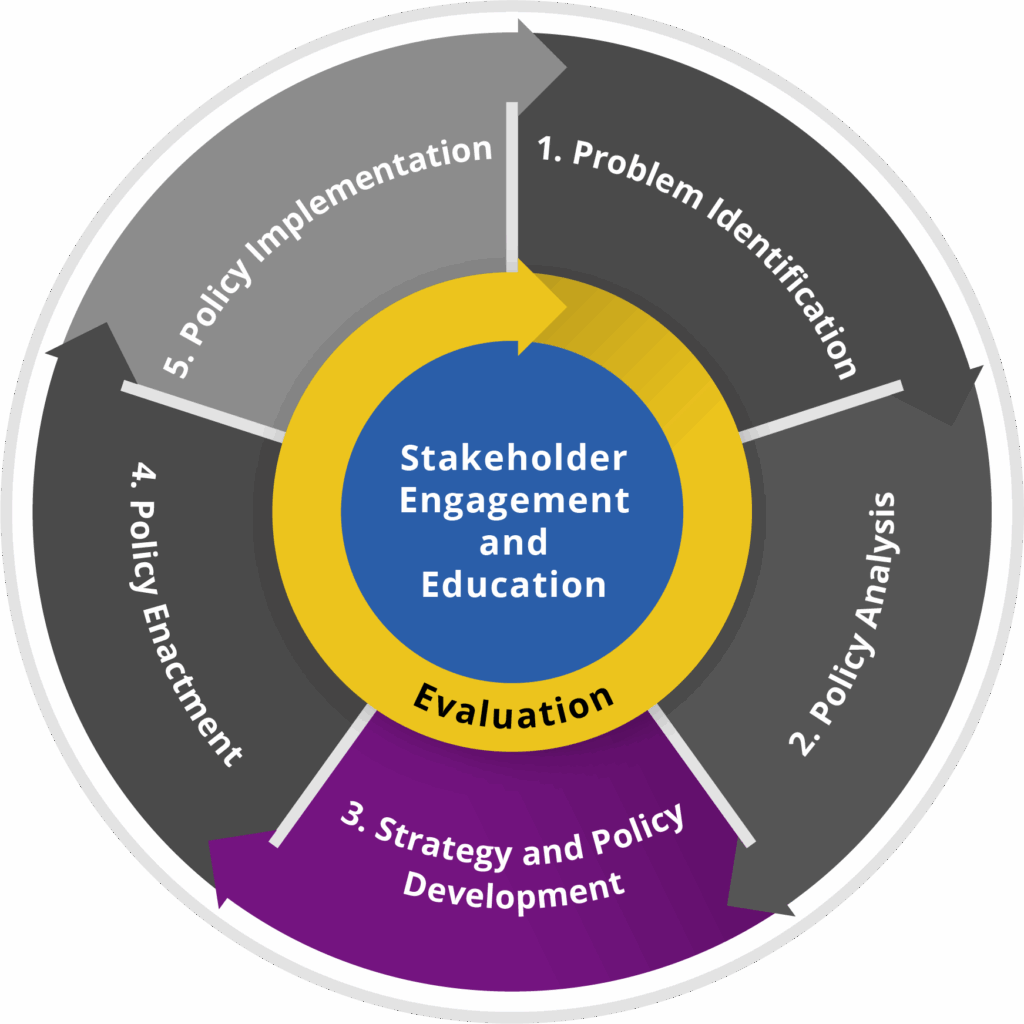
Policy Development & Implementation
The Problem:
Security and AI policies are often inconsistent, outdated, or too generic to enforce—leaving gaps across departments and audits.
Our Approach:
We deliver customized, audit-ready policies:
Mapped to your real business use cases
Built on best-practice templates (ISO, NIST, CIS, NIST AI RMF)
Delivered with full implementation and staff training support
How It Helps:
Provides defensible documentation that’s easy to adopt and enforce—improving compliance and culture.
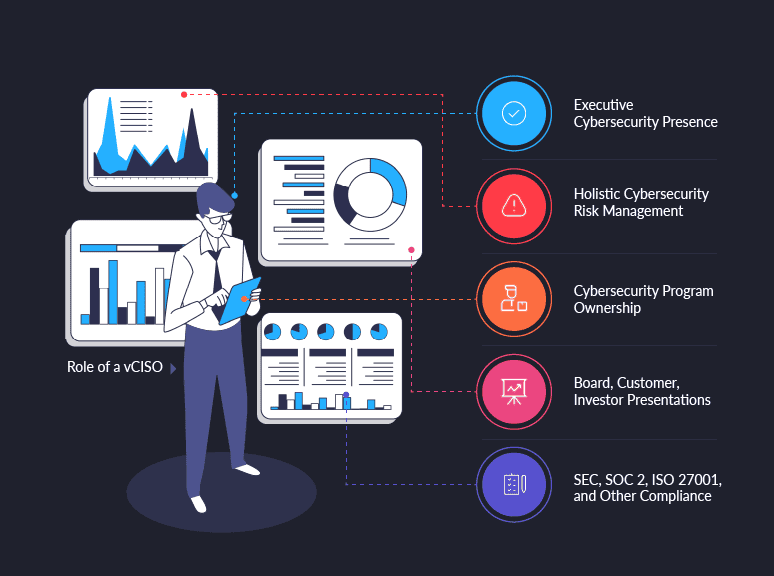
vCISO / Fractional CISO
The Problem:
Not every organization can justify a full-time CISO, but many need strategic security leadership to mature their programs.
Our Approach:
Symosis provides vCISO support with:
Embedded CISO-level leadership
Board and executive reporting
Program development, oversight, and staffing guidance
How It Helps:
You get top-tier security leadership, executive alignment, and program momentum—without long-term cost or complexity.
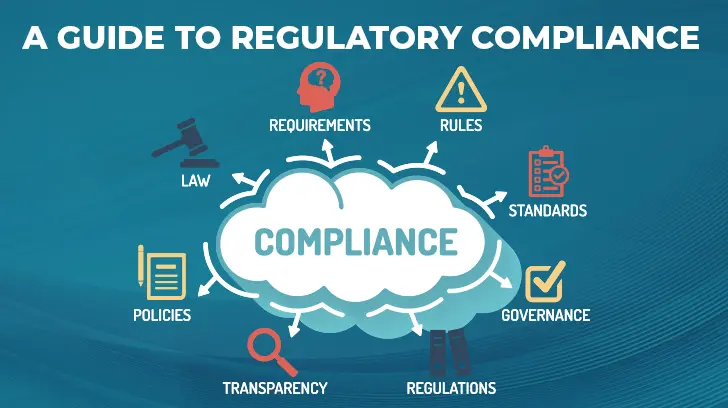
Regulatory Compliance
The Problem:
Regulatory landscapes are complex, and many orgs struggle to meet overlapping requirements across HIPAA, PCI, NIST, SOX, and others.
Our Approach:
We simplify compliance with:
Framework gap assessments and readiness reviews
Remediation planning and policy/tool alignment
Crosswalks between standards to reduce duplicate effort
How It Helps:
You stay audit-ready across multiple standards while reducing internal workload and risk exposure.
Risk Management & Third-Party Risk Management (TPRM)
The Problem:
Vendor risk is one of the top sources of breaches, yet many organizations lack a consistent onboarding, assessment, and monitoring process.
Our Approach:
Symosis delivers full TPRM lifecycle support:
Vendor intake, risk scoring, and due diligence workflows
Integration with tools like LogicManager, ServiceNow VRM, or custom dashboards
Ongoing risk mitigation and documentation
How It Helps:
Reduces third-party risk, improves contract compliance, and enables faster vendor onboarding with clear audit trails.

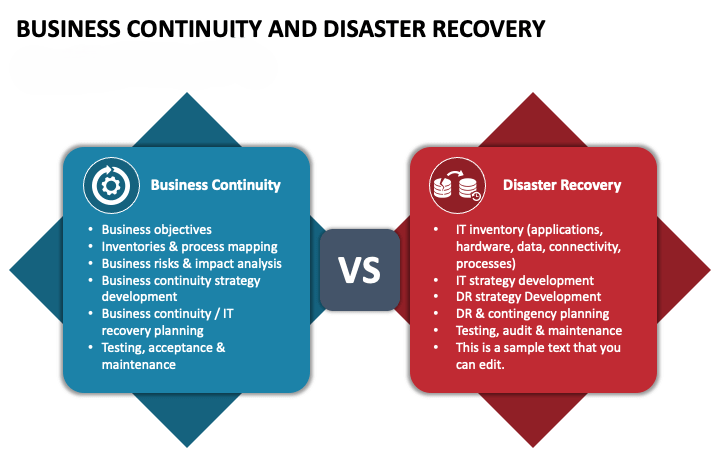
Business Continuity & Disaster Recovery (BCP/DR)
The Problem:
Organizations often don’t test or maintain recovery plans—leaving critical operations vulnerable to downtime.
Our Approach:
We build and validate continuity programs through:
Playbook creation for critical business functions
RTO/RPO definition and asset prioritization
Tabletop exercises and stakeholder walkthroughs
How It Helps:
Minimizes downtime and revenue loss during crises and demonstrates organizational preparedness.
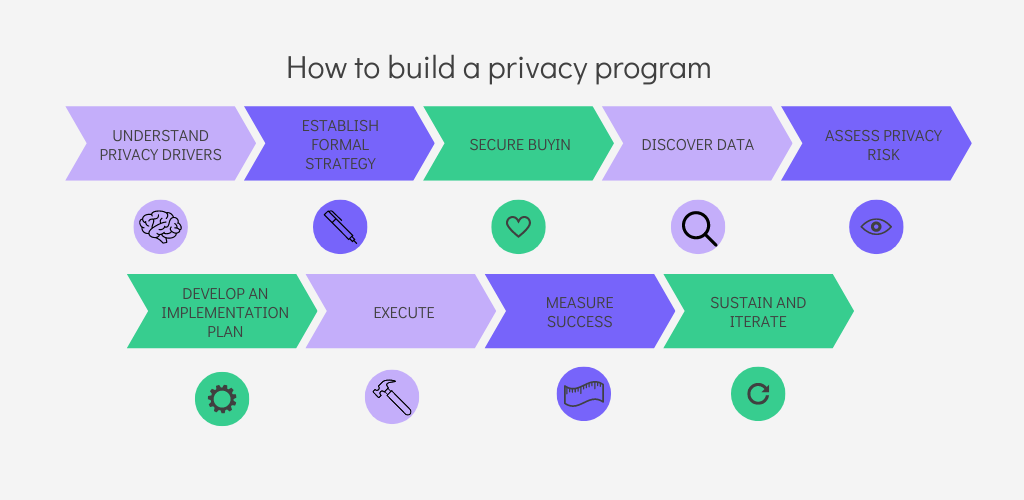
Privacy Programs
The Problem:
Data privacy laws (CCPA, GDPR, HIPAA) are evolving fast, but many teams lack scalable ways to manage data use, mapping, or impact modeling.
Our Approach:
We operationalize privacy by:
Designing privacy programs and governance workflows
Performing data mapping, DPIAs, and PIA reviews
Embedding controls in AI, SaaS, and data lifecycle tools
How It Helps:
Reduces regulatory fines, improves customer trust, and enables secure data innovation.